The BB84 protocol is used to generate secure keys for cryptographic encryption. Individual photons are used, whose polarization states serve to transmit information. This is necessary because the randomness of individual photons is used to ensure secure transmission. In practice, it is very difficult to generate individual photons and even more difficult to measure them reliably. For this reason, the BB84 protocol is only carried out as a model experiment in which no individual photons are used. In this analogy experiment, the protocol can be reproduced with many photons and clearly explained.
On this page you will find all information on the structure of the modular BB84 model experiment, the special features and learning materials for use in class..
Structure
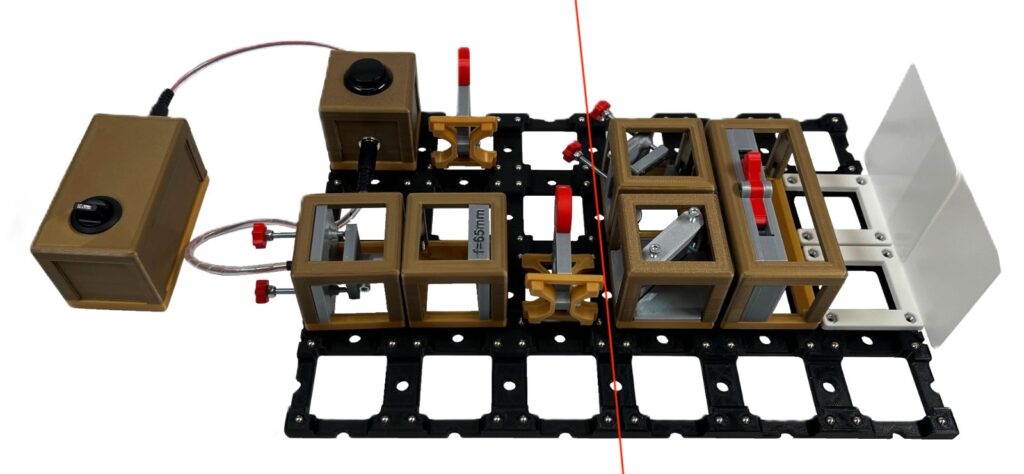
The experimental setup is divided into the transmitter Alice an the receiver Bob.
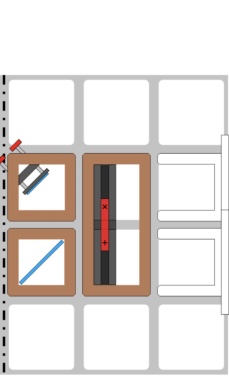
Schematic structure

Required modules:
- LED module (USB) or LED module
- Battery box
- Lens (65mm)
- Pair of basis polarizing filters
- Mirror (45°)
- Beamsplitter
- Coupled polarizing filter
- 2x screen
- Baseplate (min. 6×4)
Special Features
Preparation of a state as Alice

With the Alice transmitter’s experimental setup, it is possible to “prepare” four different polarization states. To do this, the correct polarizing filter must be positioned in the correct orientation in the light of the LED. The specific “state” that is generated in this way can be read from the polarizing filter’s markings, as shown in the figure.


Both polarizing filters can be rotated by 90° to create different states. This also makes it possible to create the states ↑〉 (or 0°) and |↖〉 (or -45°). Each polarizing filter can be used to prepare two states that are exactly orthogonal to each other. Together, two such orthogonal states are called a basis. We call the polarizing filter that can be used to generate the states |↗〉and |↖〉the X polarizing filter and the associated basis the X basis. We call the polarizing filter that can be used to generate the states |↑〉and |→〉the +-polarizing filter and the corresponding base the +-base.
Performing a measurement
Bob’s setup is designed to measure the polarization states prepared by Alice. On Bob’s side, the light first hits a beam splitter, which splits the light into two partial beams. One of the partial beams is reflected by a mirror onto the coupled polarizing filter, while the other hits the coupled polarizing filter directly. Because both the reflection at the mirror and the reflection and transmission at the beam splitter (almost) completely preserve polarization, two beams of the same polarization strike the coupled polarizing filter.
The coupled polarizing filter contains two polarizing films that are rotated 90° relative to each other. Similar to the X-polarizing filter and the +-polarizing filter, the polarization direction can be read from the grid in front of the polarizing filter.
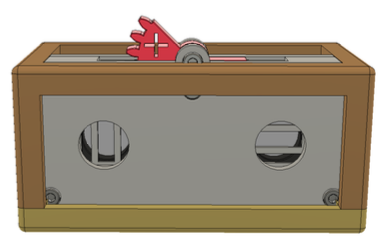

Limitations of the model
In the model, the light is split into roughly equal parts at the beam splitter. One of the polarizing filters in the coupled polarizing filter absorbs all of the light, while the second polarizing filter transmits (almost) all of the light. This second part can then be seen on the screen. In the case of a single photon, division at the beam splitter is not possible. Instead, a superposition is created, which collapses when measured at one of the polarizing filters. In the end, there is a 50% probability that the photon will be absorbed by the other polarizing filter during measurement. For this reason, a polarizing beam splitter is used instead in real experiments. This always transmits one polarization direction and always reflects the orthogonal orientation, so that there can be no problems with absorption.
Simulation of key generation according to the BB84 protocol
Exchange of Data
In the BB84 protocol, the actual information is encrypted in the form of bit values in the polarization. To do this, one of the two polarization states of a basis is assigned the bit value 1 and the other state is assigned the bit value 0, e.g.:
| Basis | Polarization | Bit |
| x | |↗〉 | 1 |
| x | |↖〉 | 0 |
| + | |↑〉 | 1 |
| + | |→〉 | 0 |
There are now two possible encodings for each bit value. This is intentional in order to generate a secure key.
A secure key
For a key to be secure, only Alice and Bob must have access to it. To achieve this, it is essential to ensure that not enough data can be intercepted from the communication between Alice and Bob to generate the complete key. Ideally, it should also be noticeable if the exchange of the key is intercepted.
The BB84 protocol achieves both of these goals. It does so by exploiting the fact that Bob measures a random result when the bases are the same. The double assignment of bit values allows both situations to occur. A secure key exchange can then take place through a random combination of both cases.
Simulation of randomness
In the model, light can be observed on both screens. This is obviously not possible in the real experiment, since the single photon cannot be measured at both detectors simultaneously. Instead, the superposition decays as a result of the measurement, and it is random at which detector the photon is measured.
This has the important consequence that Bob cannot distinguish in the real situation whether he has measured a random result as long as he does not know which base Alice used to encrypt the bit. In the model, on the contrary, this becomes immediately clear and is not random. For this reason, we have to “play dumb” during the experiment and pretend that we do not know whether the result is reliable or not. We also have to simulate randomness. Dice are used for this purpose. There is one die that can be used to select a random base and another die that can be used to randomly select the bit.
Implementation of the Protocol
In addition to the existing communication channel with single photons as information carriers, a second channel is required to implement the protocol. This channel is public and has no special technical requirements. In reality, this could be communication via the Internet, for example. In the model, the relevant information can simply be exchanged verbally.
Learning Materials
All collected working materials
Exemplary workbook for use in class (only German): Workbook BB84
